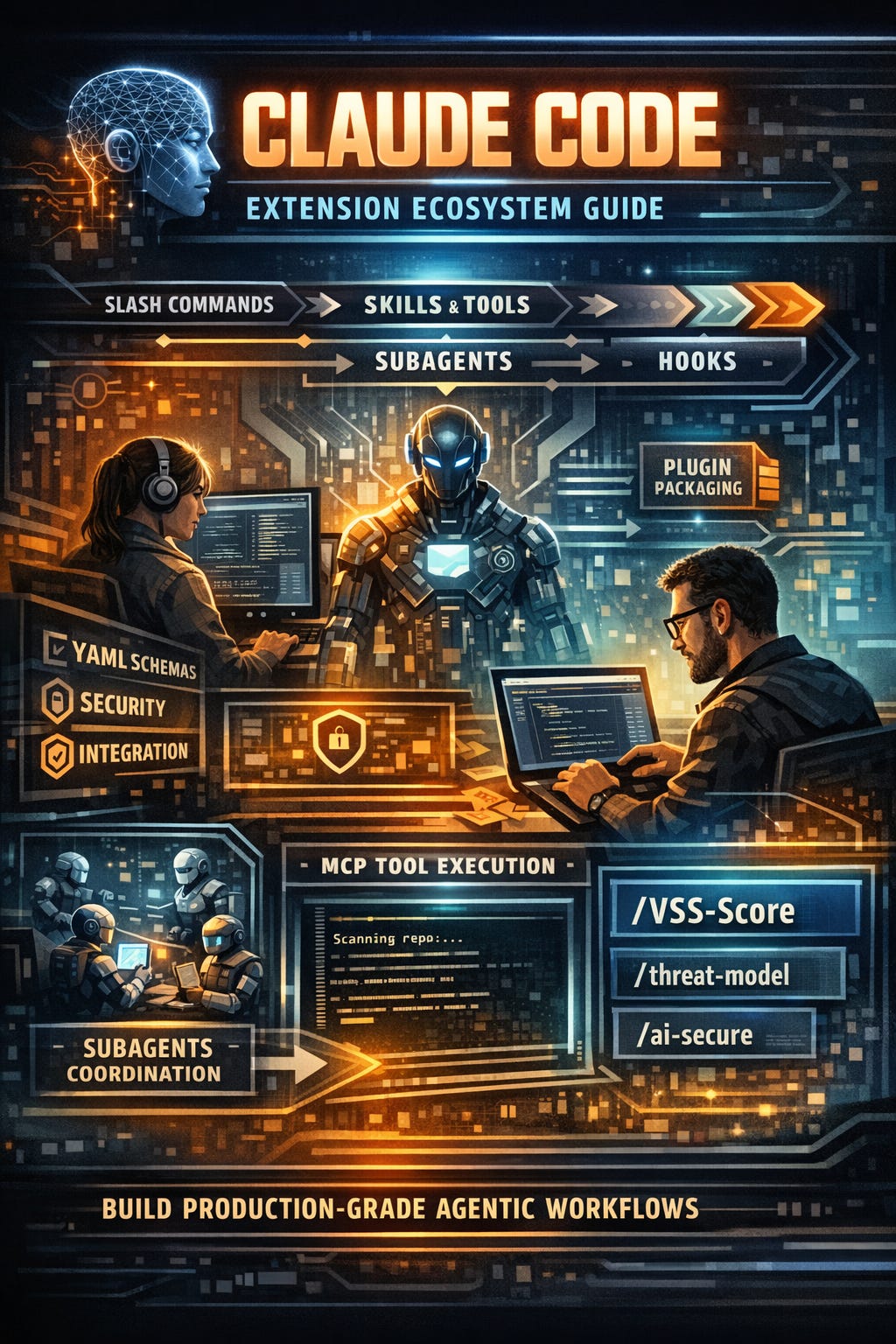
Claude Code “Extension Ecosystem”
AI Engineers building agentic systems need precise control over Claude Code’s extension ecosystem. This guide details skills, tools, plugins, hooks, subagents, and slash commands with implementation patterns, YAML schemas, security considerations, and integration strategies for production agentic workflows. All examples use Claude Code v2.3+ conventions.
Architecture Layers & Data Flow
User Input → Slash Commands → Skills (reasoning) → Tools (execution)
↕ Subagents (parallelism)
↕ Hooks (event-driven)
↓ Plugin (packaging/distribution)
Core Principle: Skills own reasoning orchestration. Tools provide scoped execution. Everything else wires the delivery system.
1. Skills: Structured Reasoning Modules
Skills define domain-specific reasoning patterns using YAML + embedded workflows. They’re the portable “agent personality” layer.
Skill Schema (skills.yaml)
id: owasp-ai-vss-scorer
version: 1.2.0
name: OWASP AI VSS Vulnerability Scorer
description: Scores AI system components per OWASP AI VSS methodology
triggers:
- pattern: “(score|vss|vulnerability).*ai”
- pattern: “threat model.*(llm|agent)”
role: “You are an OWASP AI VSS expert. Score vulnerabilities using CVSS-like methodology.”
workflow:
- step: identify_assets
description: “Extract AI components: models, prompts, tools, data flows”
tools: [”repo_search”, “file_read”]
- step: score_vulnerabilities
description: “Apply VSS Base/Threat/Temporal metrics”
template: |
VSS Score: {{ vss_base }} ({{ vector }})
Mitigation: {{ mitigations }}
- step: generate_report
format: markdown
tools: [”jira_create”, “slack_notify”]
constraints:
- NEVER execute untrusted code
- Require explicit approval for API mutations