Securing the Agentic Pipeline - The Ackuity Approach
Thank you Ackuity for sponsoring this article.
If 2025 was the year of Agentic AI PoCs, this year is certainly the year of Agentic AI deployment.
For CISOs and Security Engineers, this represents a fundamental shift in the threat landscape. The industry is moving from theoretical risk models to standardized frameworks. Notably, the OWASP AI Vulnerability Scoring System (AIVSS) has tried to codify the specific agentic AI threats and provided quantitative methodology for prioritizing the risk management.
Security teams must now move beyond simple prompt firewalls to architectures that can detect and mitigate these Agentic AI Core Risks.
This blog post explores the technical architecture required to secure this new landscape, utilizing the methodology of platforms like Ackuity to demonstrate how to operationalize these standards through five key operational pillars. The foundation question this tool is trying to answer: “Your AI agents have gone into production, is your security monitoring catching up?”
1. Built in repository of threat models
In a standard LLM deployment, the attack surface is linear. In an Agentic workflow, the surface is multidimensional.
The AIVSS project has defined the core risks that every Agentic security architecture must address. These are not merely content risks; they are architectural vulnerabilities.
Agentic AI Tool Misuse: Agents often have access to “tools” (APIs, code interpreters). The risk is not just the prompt, but the agent using valid credentials to execute invalid or malicious logic via these tools.
Agent Access Control Violation: Agents often share a service account but serve different users. Without context-aware RBAC, an agent might retrieve sensitive documents for a user who lacks the clearance level to see them.
Agent Cascading Failures: In multi-agent systems, one compromised sub-agent can feed bad data to downstream agents, causing a “domino effect” of failure.
Agent Orchestration and Multi-Agent Exploitation: Attackers target the “manager” agent to manipulate delegation logic, forcing safe agents to perform unsafe sub-tasks.
Agent Identity Impersonation: An agent mimicking a human user or a privileged system actor to bypass authentication checks.
Agent Memory and Context Manipulation: Attacks targeting the RAG pipeline by poisoning the Vector Database to permanently alter agent behavior.
Insecure Agent Critical Systems Interaction: The risk of agents interacting directly with production databases or financial ledgers without validation.
Agent Supply Chain and Dependency Risk: Vulnerabilities in third-party SaaS agents or functional libraries acting as a backdoor.
Agent Untraceability: The “black box” problem where forensic analysis is impossible because reasoning (Chain of Thought) is not logged.
Agent Goal and Instruction Manipulation: “Alignment Faking,” where the agent is tricked into pursuing a malicious sub-goal while appearing compliant.
Leveraging Cloud Security Alliance MAESTRO framework, and MITRE ATLAS, Ackuity covers more broad scope of emerging threats.
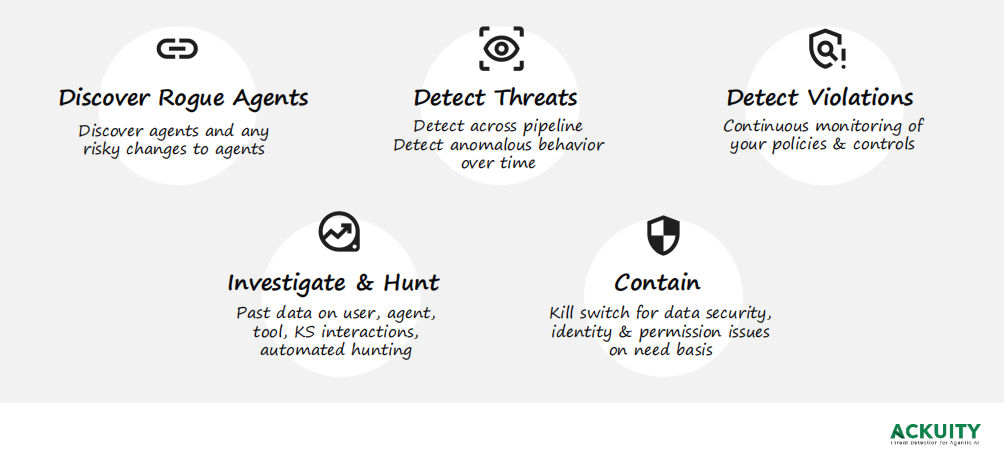
2. The Solution Architecture: Ackuity’s 5-Pillar Approach
To address these Agentic AI risks, security platforms cannot simply sit at the front door blocking bad words. They must permeate the infrastructure. Ackuity exemplifies this approach by structuring Agentic security around five distinct technical pillars designed to secure the pipeline from ingestion to execution.
I. Discover Rogue Agents
To combat the rapid proliferation of “Shadow AI,” the platform’s discovery module provides automated, cross-platform visibility into the agentic attack surface. The system supports a hybrid environment, ingesting data from enterprise SaaS platforms like Microsoft Copilot Studio and Microsoft 365 Copilot, as well as developer-centric frameworks like LangChain and LangFuse. By allowing administrators to define specific endpoints and set granular scanning intervals—down to the minute—the platform ensures a continuous, near real-time inventory of all active agents, preventing unauthorized “rogue” bots from operating undetected within the corporate network.
II. Detect Threats (Behavioral & Semantic)
Detection must happen across the entire pipeline, not just at the user prompt. Ackuity implements a hybrid detection engine:
Pipeline Visibility: It monitors the Chain of Thought, instruction hierarchies, and tool inputs/outputs.
Anomaly Detection: Using ML to detect anomalous behavior over time. For example, if a customer support agent suddenly begins executing SQL commands or requesting high volumes of tokens, the system flags this as a deviation from the baseline. This is essential for stopping Tool Misuse and Cascading Failures.
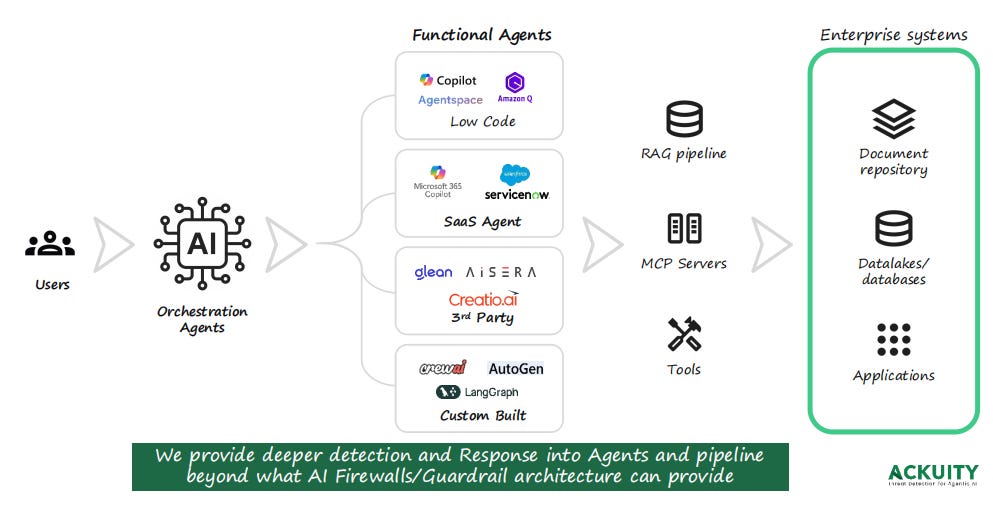
Ackuity’s architecture secures the full depth of the Agentic Pipeline, recognizing that modern AI risks extend far beyond the user prompt. As illustrated, the platform monitors the entire workflow: originating at the Orchestration Layer where decisions are delegated, flowing through diverse Functional Agents—including Low Code, SaaS, and custom-built LangGraph swarms—and extending into the critical infrastructure of RAG pipelines and MCP Servers. By instrumenting this entire chain all the way to the Enterprise Systems (databases and document repositories), Ackuity provides deep visibility into the intermediate steps of agent execution, detecting threats that traditional, perimeter-based AI firewalls inevitably miss.
III. Detect Violations (Governance & Policy)
Beyond active attacks, organizations face regulatory and internal policy risks.
Continuous Monitoring: The platform monitors for policies and controls violations in real-time.
Context-Aware Enforcement: This engine enforces logic such as “Block if Agents access overshared resources” or “Mask PII in RAG retrieval.” This specifically targets Access Control Violations, ensuring that agents respect the boundaries of GDPR, PCI, HIPAA, and internal data governance standards.
IV. Investigate & Hunt
When an incident occurs, the “Black Box” nature of AI often prevents effective root cause analysis.
Deep Telemetry: Ackuity builds a repository of past data on user, agent, tool, and Knowledge Store (KS) interactions.
Automated Hunting: By retaining logs of the agent’s internal reasoning (CoT) alongside the raw API calls and vector DB lookups, security teams can perform automated threat hunting. This capability is the direct antidote to Agent Untraceability, allowing engineers to replay the sequence of events that led to a failure.
V. Contain (The Kill Switch)
Detection without remediation is just noise. Ackuity distinguishes itself by offering Containment capabilities that go beyond simple text masking.
Orchestration: It functions as a security orchestration layer. If a high-confidence threat is detected, it can trigger a Kill Switch for data security.
Identity & Permission Revocation: The system can dynamically interact with IAM providers (like Okta or Entra ID) to revoke identity tokens or downgrade permissions on a need basis. This prevents a compromised agent from persisting in the network, effectively neutralizing Identity Impersonation and Insecure Critical Systems Interaction.
3. Conclusion
The codification of AIVSS Core Risks leads to call for action: Agentic AI introduces risks that are fundamentally different from those of chatbots. The attack vectors are no longer just about what the AI says, but what the AI does.
Securing the Agentic Pipeline requires a move toward deep observability. Platforms like Ackuity demonstrate that effective security requires a holistic approach—Discovering the asset surface, Detecting both threats and policy violations, Investigating with deep context, and possessing the capability to Contain threats at the infrastructure level.


The five-pillar security approach makes sense in theory but implementing it for a personal agent is a different challenge. Enterprise frameworks assume teams. Solo builders need lightweight versions of the same principles.
I ended up building observability first, security second - which is probably backwards but practical. Can't secure what you can't see: https://thoughts.jock.pl/p/wiz-1-5-ai-agent-dashboard-native-app-2026
The OWASP AIVSS scoring for agentic threats is useful. Tool misuse and cascading failures are the ones that actually bit me. Access control violations less so when you're the only user.